Introduction
In modern cloud architectures, Azure Private Endpoint plays a critical role in ensuring that security is no longer optional—it’s foundational. As organizations move workloads to the cloud, one of the biggest challenges is how to securely access Azure services without exposing them to the public internet.
How do you securely access Azure services without exposing them to the public internet?
That’s where Azure Private Endpoint comes in.
Azure Private Endpoint is part of Azure Private Link, enabling private, secure, and isolated connectivity between your virtual network and Azure services.
What is Azure Private Endpoint?
Azure Private Endpoint is one of the most important building blocks in modern cloud networking and security architecture. To truly understand it, you need to think beyond just definitions and see how networking, identity, DNS, and routing all come together.
Think of it as:
“Bringing Azure services inside your private network.”
So, An Azure Private Endpoint is a network interface (NIC) that is created inside your Virtual Network (VNet) and assigned a private IP address from your subnet.
This NIC acts as a private entry point to a specific Azure resource (like Storage, SQL Database, Key Vault, etc.), enabling secure connectivity via Azure Private Link.
Unlike traditional access methods, this connection:
- Is fully contained within Microsoft’s private backbone network
- Does not use public IPs
- Does not traverse the internet
Key Definition:
- Uses private IP from your VNet
- Connects to Azure services securely via Private Link
- Eliminates exposure to the public internet
Breaking Down the Definition
1. “Network Interface (NIC) inside your VNet”
A Private Endpoint is literally an Azure-managed NIC placed inside your subnet.
- It behaves like:
- A VM NIC
- With an IP address from your subnet
- But instead of connecting to a VM, it connects to an Azure PaaS service
Important:
This NIC is owned and managed by Azure, but lives in your network boundary
2. “Gets a Private IP Address”
When you create a Private Endpoint:
- Azure assigns:
- A private IP (e.g., 10.x.x.x)
- This IP belongs to:
- Your subnet CIDR range
Example:
- Subnet:
10.10.1.0/24 - Private Endpoint IP:
10.10.1.5
This means:
✔ Your application sees the service as local network traffic
✔ No NAT to public IP is required
3. “Connects to Azure Services via Private Link”
This is where the magic happens.
Azure Private Endpoint uses Private Link, which:
- Creates a secure mapping between:
- Your Private Endpoint (NIC)
- Azure service backend
Important insight:
You are not directly connecting to the service instance
You are connecting to a privately exposed endpoint of that service
4. “Eliminates Exposure to Public Internet”
Traditionally, Azure services are accessed like this:
mystorageaccount.blob.core.windows.net → Public IPWith Private Endpoint:
mystorageaccount.blob.core.windows.net → Private IP (via DNS override)✔ No public IP exposure
✔ No internet routing
✔ No attack surface from outside
The Mental Model (VERY IMPORTANT)
Think of Azure Private Endpoint like this:
Instead of your application going out to the internet to reach Azure services…
Azure services are brought inside your private network boundary
Analogy
Imagine:
- Azure service = Bank building
- Internet = Public road
- Private Endpoint = Private tunnel
Without Private Endpoint:
- You travel on public roads → exposed → less secure
With Private Endpoint:
- A secure underground tunnel connects your house to the bank
No one else can see or access that path
How It Works (Conceptual Flow)
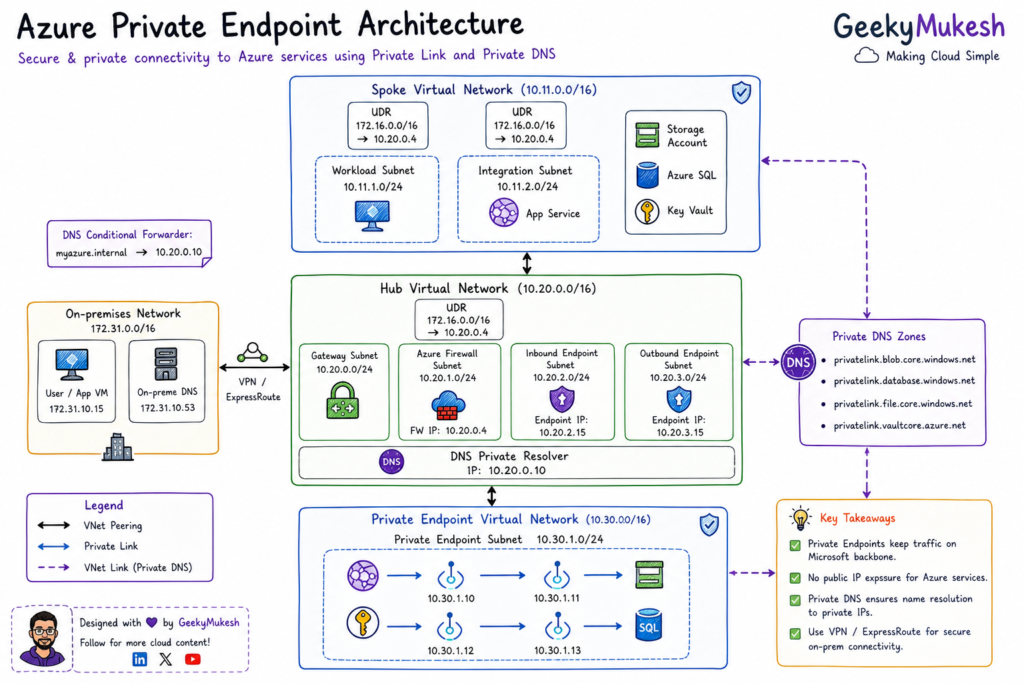
In most enterprise environments, Azure Private Endpoint is implemented using a centralized networking model. You can explore this in detail in our Hub-and-Spoke architecture guide, where we explain how VNets are designed for scalable and secure communication.
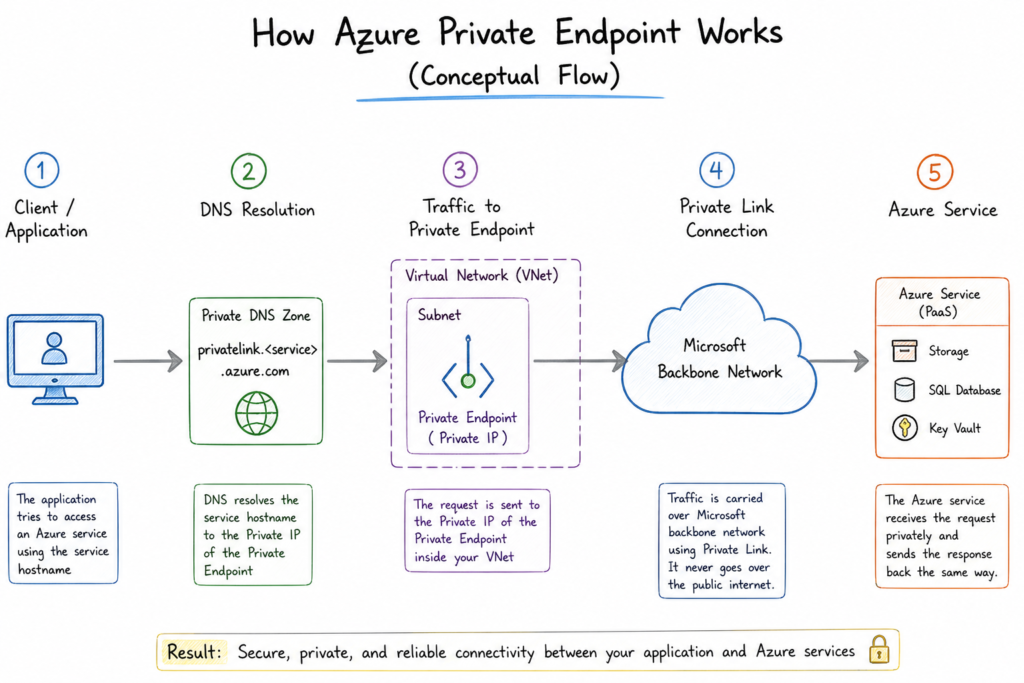
Step-by-step flow:
- You create a Private Endpoint in your subnet
- Azure assigns it a private IP address
- It connects to a specific Azure resource (e.g., Storage, SQL)
- Traffic flows through:
- Microsoft backbone network
- NOT the public internet
- DNS resolves the service to the private IP
or we can say:
1. Application Initiates Request
- Uses standard FQDN:
mystorageaccount.blob.core.windows.net2. DNS Resolution Happens
- Public DNS is overridden by:
privatelink.blob.core.windows.net- Returns:
10.10.1.5 (Private Endpoint IP)3. Traffic Routed Inside VNet
- Packet goes to:
Private Endpoint NIC (10.10.1.5)4. Private Link Takes Over
- Azure internally maps:
Private Endpoint → Azure Service Backend- Traffic flows via:
Microsoft backbone network
5. Azure Service Responds
- Response returns via same private path
- No internet involvement
Security Deep Dive
Private Endpoint significantly improves security:
✔ Removes Public Attack Surface
- No exposed endpoints
- No brute-force or DDoS from internet
✔ Enables Zero Trust Architecture
- Only private network access allowed
✔ Works with NSG & Firewall
- You can:
- Restrict subnet access
- Control traffic flow
DNS – The Hidden Backbone
Private Endpoint heavily depends on DNS.
Why?
Because:
- Clients still use same public hostname
- But DNS resolves it to private IP
Without correct DNS:
Traffic may go to public endpoint
Real-World Example
Let’s say:
- App running in VNet
- Needs to access Azure SQL
If you are deploying containerized applications, integrating Azure Private Endpoint with Kubernetes can significantly improve security. In our Kubernetes learning series, we cover how modern workloads can securely communicate with Azure services.
Without Private Endpoint:
- Connects via public IP
- Requires firewall rules
With Private Endpoint:
- Connects to:
10.10.2.4 (Private IP)✔ No firewall exposure
✔ Fully private communication
Important Things Most People Miss
1. It’s NOT Just Networking
- Also involves:
- DNS
- Identity
- Service configuration
2. One Endpoint per Subresource
Example (Storage):
- Blob → separate endpoint
- File → separate endpoint
3. Approval May Be Required
- Cross-subscription scenarios:
- Need manual approval
4. It’s Regional
- Private Endpoint is tied to:
- A specific Azure region
Key Takeaways
- Private Endpoint = Private IP + NIC + Service Mapping
- It changes:
- How traffic flows
- How services are exposed
- It is a core part of:
- Zero Trust Networking
- Secure Cloud Architecture
Why Use Private Endpoint?
1. Enhanced Security
- No public exposure
- Traffic stays inside Azure backbone
- Ideal for sensitive workloads (finance, healthcare)
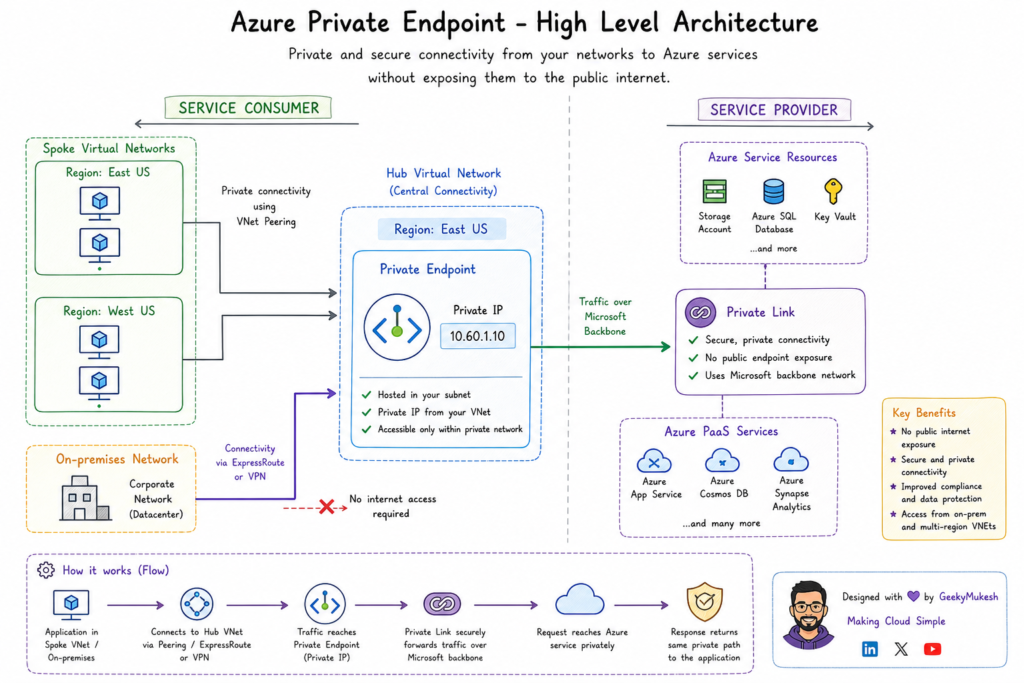
2. Private Connectivity
- Access from:
- Azure VNet
- On-premises (via VPN/ExpressRoute)
3. Better Performance
- Reduced latency
- No internet routing
4. Compliance Ready
- Helps meet regulatory requirements
Private Endpoint vs Service Endpoint
This is one of the most important interview + real-world topics 👇
| Feature | Private Endpoint | Service Endpoint |
|---|---|---|
| IP Type | Private IP inside VNet | Public IP |
| Security | Fully private | Public endpoint (restricted) |
| Scope | Specific resource instance | Entire Azure service |
| Cost | Paid | Free |
| Access | From VNet + On-prem | Only from VNet |
Key Insight:
- Private Endpoint = Zero public exposure
- Service Endpoint = Secure but still public-facing
Azure Private Link vs Private Endpoint
- Private Link → The technology/framework
- Private Endpoint → The actual connection (NIC)
In simple terms:
Private Link is the road, Private Endpoint is the vehicle
Supported Azure Services
Private Endpoints work with many services:
- Azure Storage
- Azure SQL Database
- Azure Cosmos DB
- Azure Key Vault
- Azure App Services
- Azure Functions
Most modern Azure PaaS services support it.
Components of Private Endpoint Architecture
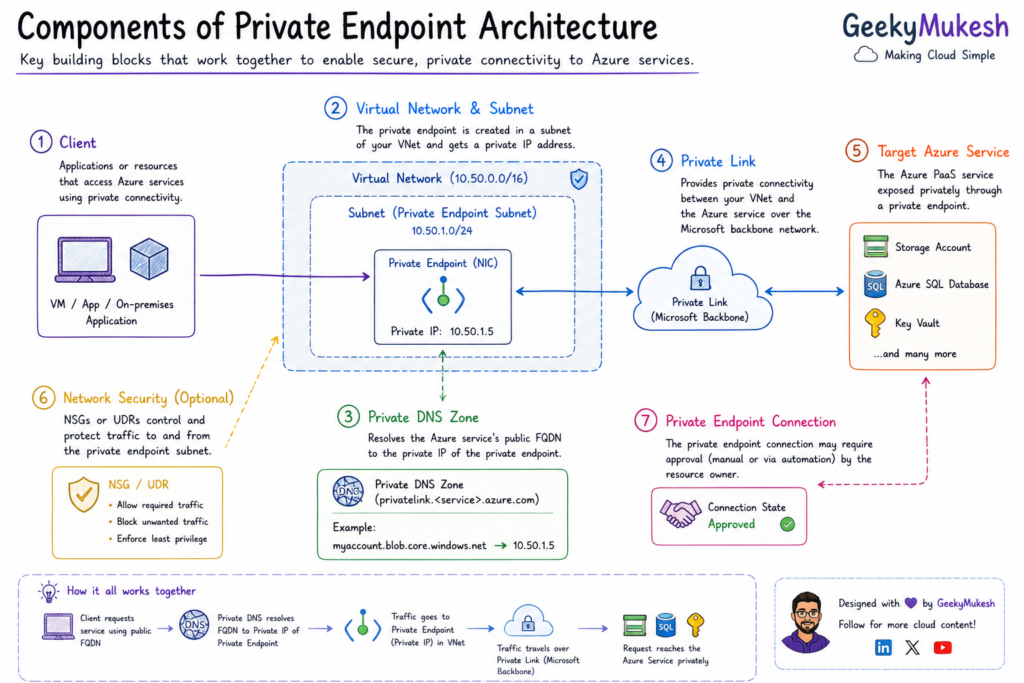
Core Components:
To properly design and operate Azure Private Endpoints, you must understand how each component works individually and together. These are not just building blocks—they form a tightly coupled system of networking + DNS + service mapping.
1. Virtual Network (VNet)
The Virtual Network (VNet) is the foundation layer where your Private Endpoint exists. It represents your isolated, logically segmented network inside Azure, similar to a traditional data center network.
What it does:
- Provides private IP address space
- Enables secure communication between resources
- Acts as the boundary of trust
In context of Private Endpoint:
- The Private Endpoint NIC is deployed inside a VNet
- All traffic to the Azure service flows within this network boundary
Key Characteristics:
- Uses CIDR ranges (e.g.,
10.10.0.0/16) - Can be connected to:
- Other VNets (VNet Peering)
- On-premises networks (VPN / ExpressRoute)
Important Considerations:
- Choose non-overlapping IP ranges (critical in hybrid setups)
- Plan for scalability (future endpoints, services)
Best Practice:
Use a Hub-Spoke architecture, where Private Endpoints often reside in a centralized or spoke VNet depending on design.
2. Subnet
A Subnet is a segmented portion of your VNet where Azure resources are deployed—including Private Endpoints.
What it does:
- Divides VNet into logical segments
- Controls:
- IP allocation
- Security policies (NSG, UDR)
In context of Private Endpoint:
- The Private Endpoint NIC is created inside a subnet
- Azure assigns a private IP from this subnet
Dedicated Subnet – Why Recommended?
Although not mandatory, it is strongly recommended to use a dedicated subnet for Private Endpoints.
Benefits:
- Better traffic isolation
- Easier network security control
- Cleaner routing policies
- Avoid conflicts with other resources
Special Behavior:
- Network policies (NSG/UDR) may behave differently:
- By default, some policies are disabled for Private Endpoints
- You can enable them manually if needed
Best Practice:
Create a subnet like:
private-endpoint-subnet (e.g., 10.10.2.0/24)3. Private Endpoint (NIC)
This is the heart of the architecture.
A Private Endpoint is an Azure-managed Network Interface (NIC) that connects your VNet to a specific Azure service.
What it does:
- Acts as a private access point
- Gets a private IP from your subnet
- Maps to an Azure service via Private Link
Internally:
- It is not a VM, but behaves like a NIC
- Azure handles:
- Routing
- Connectivity
- Mapping to backend service
Key Features:
- Assigned static private IP
- Bound to:
- A specific resource
- A specific subresource
Subresource Concept (VERY IMPORTANT)
For many services, you must specify subresources:
| Service | Subresources |
|---|---|
| Storage | blob, file, queue, table |
| SQL | sqlServer |
| Key Vault | vault |
Each subresource may require a separate Private Endpoint
Important Notes:
- Cannot be shared across multiple resources
- Requires approval in some cases
- Region-specific resource
Think of it as:
A private doorway from your VNet into an Azure service
4. Target Resource (Azure Service Instance)
This is the actual Azure service you want to access privately.
Examples:
- Azure Storage Account
- Azure SQL Database
- Azure Key Vault
- Azure Cosmos DB
What changes with Private Endpoint?
Normally:
- Service is exposed via public endpoint
With Private Endpoint:
- Service is:
- Still public internally
- But privately exposed to your VNet
Important Behavior:
- You can:
- Disable public access completely
- Allow access only via Private Endpoint
Security Impact:
- Reduces attack surface
- Prevents:
- Data exfiltration
- Unauthorized access
Gotcha:
- Access is tied to:
- Specific resource instance
- Not entire service
Real Insight:
Private Endpoint does NOT move the service into your VNet—it projects a private interface into your VNet
5. Private DNS Zone
This is one of the most critical and often misunderstood components.
Without DNS, Private Endpoint simply won’t work as expected.
What it does:
- Resolves Azure service hostname → Private IP
- Overrides public DNS resolution
How it works:
When you access:
mystorage.blob.core.windows.netDNS translates it to:
10.10.2.5 (Private Endpoint IP)Azure automatically uses zones like:
| Service | Private DNS Zone |
|---|---|
| Storage | privatelink.blob.core.windows.net |
| SQL | privatelink.database.windows.net |
| Key Vault | privatelink.vaultcore.azure.net |
VNet Linking
Private DNS Zone must be:
- Linked to your VNet
Otherwise:
DNS resolution fails
Traffic goes to public endpoint
Common Mistakes:
- Forgetting DNS zone linking
- Using custom DNS without forwarding rules
- Mixing public + private DNS incorrectly
Best Practice:
Always use:
- Azure Private DNS Zones
- Or configure conditional forwarding (on-prem DNS → Azure DNS)
DNS Behavior (VERY IMPORTANT)
DNS plays a critical role.
What happens:
- Public DNS → resolves to public IP
- Private DNS → resolves to private IP
Azure automatically creates:
privatelink.<service>.azure.comExample:
mystorage.blob.core.windows.net → private IPIf DNS is misconfigured:
Your traffic may go to public endpoint
Communication Flow
- Client connects using same connection string
- DNS redirects to private IP
- Traffic flows internally
No code changes required!
Real Use Cases
Azure Private Endpoint is not just a feature—it’s a core security pattern used across industries where data protection, compliance, and controlled access are critical.
If you are deploying containerized applications, integrating Azure Private Endpoint with Kubernetes can significantly improve security. In our Kubernetes learning series, we cover how modern workloads can securely communicate with Azure services.
1. Banking Applications
A banking application processes:
- Customer transactions
- Account balances
- Payment data
These systems typically rely on:
- Azure SQL Database
- Azure Key Vault
- Storage Accounts
Problem Without Private Endpoint:
- Databases exposed via public endpoints
- Requires:
- IP whitelisting
- Firewall rules
- Still vulnerable to:
- Misconfigurations
- Data exfiltration risks
Solution with Private Endpoint:
- Azure SQL is accessed via:
- Private IP inside VNet
- Public access is:
- Disabled completely
Security Benefits:
- No internet exposure
- Internal-only communication
- Supports Zero Trust architecture
Real-World Insight:
Many financial institutions mandate that no database should be accessible over public IP, making Private Endpoint a compliance requirement.
2. Healthcare Systems
Healthcare systems store:
- Patient records (EHR/EMR)
- Diagnostic data
- Sensitive personal information
Regulatory Requirements:
- HIPAA (US)
- GDPR (EU)
- Local data protection laws
These require:
- Data not exposed to public internet
- Strong access control
Solution with Private Endpoint:
- Services like:
- Azure Storage (for medical files)
- Key Vault (for encryption keys)
- Are accessed via:
- Private network only
Security Advantages:
- Ensures data stays within trusted network boundary
- Prevents accidental exposure
- Enables audit-friendly architecture
Real-World Insight:
In healthcare, even a temporary public exposure can lead to compliance violations—Private Endpoint minimizes this risk.
3. Hybrid Architecture
On-prem → Azure securely
Organizations running:
- Legacy systems on-premises
- Modern workloads in Azure
Need:
Secure communication between both environments
Traditional Approach:
- Access Azure services via:
- Public endpoints over internet
- Issues:
- Security concerns
- Compliance challenges
Solution with Private Endpoint:
- On-premises connects via:
- VPN or ExpressRoute
- Access Azure services using:
- Private IPs
Flow:
On-Prem → VPN/ExpressRoute → VNet → Private Endpoint → Azure ServiceBenefits:
- No internet traversal
- Unified network architecture
- Works like extended data center
Real-World Insight:
This is heavily used in enterprise migrations, where companies move gradually to Azure without exposing services publicly.
4. Storage Isolation
Blob storage without public access
Applications store:
- Logs
- Backups
- Data lake files
- Sensitive documents
Problem Without Private Endpoint:
- Storage accounts exposed via:
- Public endpoint
- Even with firewall:
- Risk of misconfiguration
Solution with Private Endpoint:
- Blob storage is:
- Accessible only via private IP
- Public access:
- Completely disabled
Benefits:
- Prevents:
- Data leaks
- Unauthorized downloads
- Ensures:
- Internal-only access
Advanced Use Case:
- Secure data lake architectures
- Restrict access to:
- Specific VNets only
Real-World Insight:
Many organizations now enforce:
“Storage accounts must not have public access enabled”
Step-by-Step: Create Private Endpoint (Simplified)
Using Azure CLI:
az network private-endpoint create \
--name myPE \
--resource-group myRG \
--vnet-name myVnet \
--subnet mySubnet \
--private-connection-resource-id <resource-id> \
--group-ids blob \
--connection-name myConnectionSteps:
- Create VNet + Subnet
- Create Private Endpoint
- Approve connection
- Configure DNS
- Disable public access (optional but recommended)
Pricing Considerations
- Private Endpoint = charged per endpoint
- Data transfer charges apply
Trade-off:
Higher security
Slight extra cost
Important Limitations & Gotchas
1. One Endpoint per Resource Type
Example:
- Blob → 1 endpoint
- File → another endpoint
2. DNS Complexity
- Biggest challenge in real-world setups
3. Network Routing Behavior
- Traffic may bypass firewall in some architectures
4. Regional Dependency
- Private endpoints are regional resources
Architecture Best Practices
Use Hub-Spoke Model
- Centralized networking
Use Private DNS Zones
- Avoid manual DNS configs
Disable Public Access
- Force private connectivity
Least Privilege Access
- Restrict endpoints per resource
Advanced Scenario: Hybrid Connectivity
You can connect:
- On-prem → VPN → VNet → Private Endpoint → Azure Service
This enables fully private enterprise architecture
Key Takeaways
- Private Endpoint = Private IP for Azure services
- Eliminates public exposure
- Requires proper DNS setup
- More secure than Service Endpoints
- Core building block for Zero Trust architecture
Conclusion
Azure Private Endpoint is a game-changing feature in cloud networking. It transforms how we think about security by:
✔ Removing public exposure
✔ Enabling private communication
✔ Supporting enterprise-grade architectures
If you’re building secure, scalable, and production-ready systems in Azure, mastering Private Endpoints is non-negotiable.
New to automation? Start with our Python Programming Series—learn from scratch and build real-world cloud automation projects step by step.


Leave a Reply