1️⃣ Executive Summary
Organizations using Microsoft Defender for Cloud often require centralized monitoring in SIEM platforms such as Splunk.
Microsoft provides the ability to export Defender alerts via Event Hub, and Splunk provides the Microsoft Security Add-on to ingest and parse this data.
However, confusion often arises regarding:
- Email notifications vs security alerts
- Tenant-level vs subscription-level configuration
- Permissions required
- Sourcetypes inside Splunk
- Automation at scale
This handbook provides a complete theoretical and practical guide.
2️⃣ Understanding the Products Involved
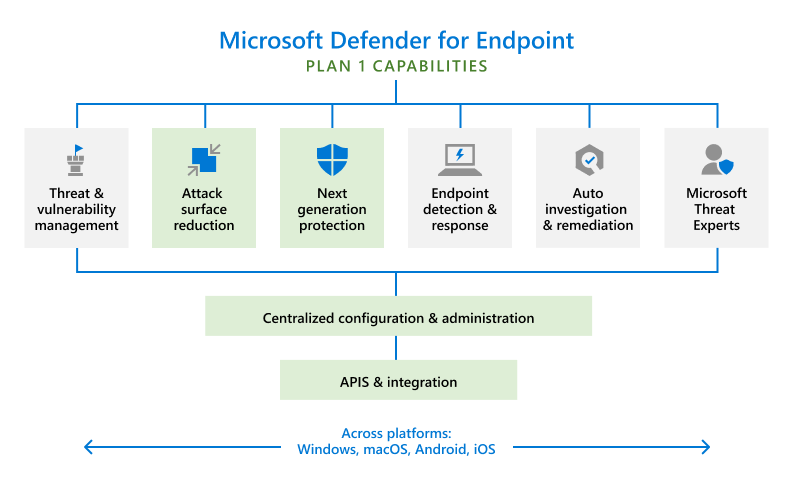
🔐 Microsoft Defender for Cloud
Microsoft Defender for Cloud
Azure-native Cloud Security Posture Management (CSPM) and Cloud Workload Protection Platform (CWPP).
It generates:
- Security Alerts
- Incidents
- Recommendations
- Secure Score updates
Important distinction:
Defender generates alerts that may trigger emails — but it does NOT expose email content as exportable logs.
📊 Splunk Microsoft Security Add-on
The Splunk documentation you referenced belongs to:
Splunk
Specifically the:
Splunk Add-on for Microsoft Security (formerly Microsoft 365 Defender Add-on)
This add-on:
- Connects to Microsoft Security APIs
- Collects data via REST APIs or Event Hub
- Maps incoming logs to predefined sourcetypes
- Normalizes data for Splunk CIM
3️⃣ Deep Dive: Splunk Documentation – Configure Permissions
This document explains how Splunk authenticates and what permissions are required.
Let’s break it down thoroughly.
🔑 Authentication Model
The add-on uses:
- Azure AD (Entra ID) App Registration
- OAuth 2.0 token-based authentication
- Microsoft Graph / Security APIs
- Event Hub consumer permissions
Two ingestion patterns exist:
1️⃣ REST API Polling
Splunk periodically calls:
- Security alerts API
- Incidents API
- Advanced hunting API
2️⃣ Event Hub Streaming
Splunk consumes Defender events pushed to Event Hub.
📌 Permissions Explained in Detail
| Permission | Purpose |
|---|---|
SecurityAlert.Read.All | Read Defender alerts |
SecurityIncident.Read.All | Read incident data |
Incident.Read.All | Access incident objects |
ThreatIntelligence.Read.All | Threat intel ingestion |
AttackSimulation.Read.All | Simulation reporting |
| Event Hub Data Receiver | Read streaming events |
These permissions are assigned to:
- App Registration
- Service Principal
- Managed Identity (depending on architecture)
Critical insight:
None of these permissions provide access to email notification bodies.
4️⃣ Deep Dive: Splunk Sourcetypes Document
This document explains how data appears once inside Splunk.
In Splunk terminology, a sourcetype defines:
- Parsing rules
- Field extraction
- Event categorization
🧾 Key Defender Sourcetypes
🔹 ms:defender:atp:alerts
Represents security alerts generated by Microsoft Defender.
Contains:
- Alert ID
- Severity
- Category
- Compromised entity
- MITRE tactics
- Status
🔹 ms365:defender:incident
Represents aggregated incident objects.
Incidents combine multiple alerts into correlated investigations.
🔹 ms365:defender:incident:alerts
Child alerts associated with incidents.
🔹 ms:defender:eventhub
Used when logs are streamed via Event Hub.
This is the most relevant sourcetype when integrating Defender for Cloud via Continuous Export.
5️⃣ Architecture Overview

Data Flow:
Microsoft Defender for Cloud ↓Continuous Export (Microsoft.Security/automations) ↓Azure Event Hub Namespace ↓Splunk Add-on (Event Hub Input) ↓Splunk Index
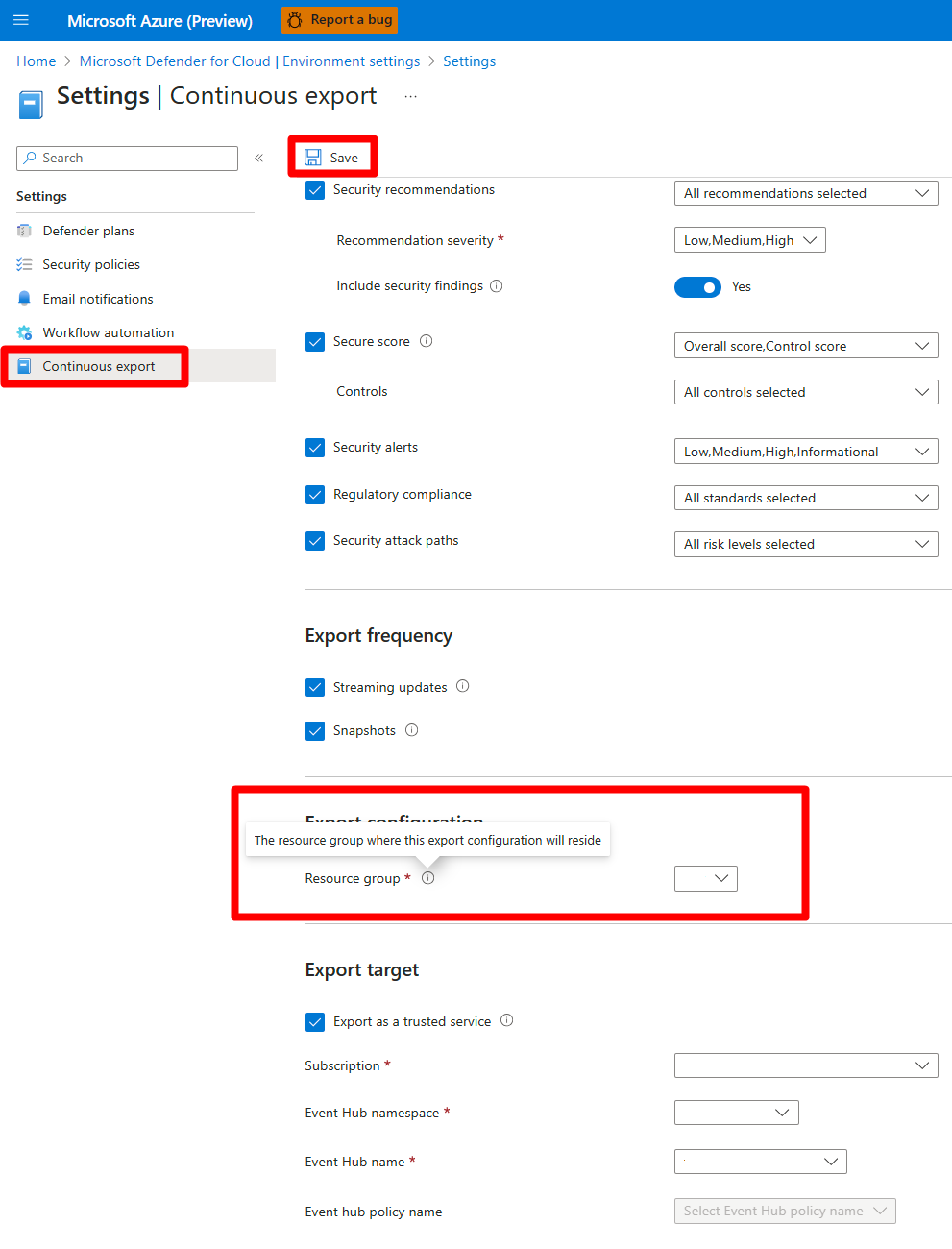
6️⃣ Continuous Export – How It Actually Works
When you enable Continuous Export, Azure creates a resource:
Microsoft.Security/automations
This resource defines:
- Scope (subscription)
- Event source (Alerts)
- Action (Event Hub destination)
In many tenants, this setting appears only at subscription level.
7️⃣ Scaling Across Multiple Subscriptions
Enterprise problem:
Continuous Export is subscription-scoped.
If you have:
- 10 subscriptions
- 50 subscriptions
- 200 subscriptions
Manual enablement is not sustainable.
8️⃣ Automation Strategy
You have three enterprise-grade approaches:
| Approach | Use Case |
|---|---|
| Terraform | Long-term governance |
| Azure Automation | Scheduled enforcement |
| Local Script | One-time rollout |
9️⃣ Practical Implementation – Python Script
This example enables Continuous Export across all subscriptions.
Install dependencies
pip install azure-identity azure-mgmt-subscription azure-mgmt-resource requests
Login
az login
Script
from azure.identity import AzureCliCredential
from azure.mgmt.subscription import SubscriptionClient
from azure.mgmt.resource import ResourceManagementClient
import requests, json
cred = AzureCliCredential()
sub_client = SubscriptionClient(cred)
API_VERSION = "2022-01-01"
LOCATION = "westeurope"
AUTOMATION_NAME = "defender-to-eventhub"
EVENTHUB_ID = "/subscriptions/<sub-id>/resourceGroups/<rg>/providers/Microsoft.EventHub/namespaces/<eh-namespace>"
for sub in sub_client.subscriptions.list():
sub_id = sub.subscription_id
print(f"Processing subscription: {sub_id}")
res_client = ResourceManagementClient(cred, sub_id)
automations = list(res_client.resources.list(
filter="resourceType eq 'Microsoft.Security/automations'"
))
if automations:
print("Already enabled")
continue
token = cred.get_token("https://management.azure.com/.default").token
url = f"https://management.azure.com/subscriptions/{sub_id}/providers/Microsoft.Security/automations/{AUTOMATION_NAME}?api-version={API_VERSION}"
payload = {
"location": LOCATION,
"properties": {
"scopes": [f"/subscriptions/{sub_id}"],
"sources": [{"eventSource": "Alerts"}],
"actions": [{
"actionType": "EventHub",
"eventHubResourceId": EVENTHUB_ID
}]
}
}
headers = {
"Authorization": f"Bearer {token}",
"Content-Type": "application/json"
}
response = requests.put(url, headers=headers, data=json.dumps(payload))
print(response.status_code)
🔟 Governance & Audit Positioning
For compliance discussions:
Defender Continuous Export is enabled programmatically across all subscriptions and monitored via Activity Logs, ensuring centralized security telemetry ingestion into Splunk SIEM.
1️⃣1️⃣ Common Misconceptions
| Myth | Reality |
|---|---|
| Splunk collects Defender emails | ❌ |
| Continuous Export available at tenant always | ❌ |
| Azure Policy can enable retroactively | ❌ |
| Event Hub streaming is near real-time | ✅ |
1️⃣2️⃣ Final Recommendations
✔ Use automation for existing subscriptions
✔ Use Azure Policy for new subscription guardrails
✔ Validate sourcetypes in Splunk
✔ Monitor Event Hub metrics
🎯 Conclusion
Integrating Microsoft Defender for Cloud with Splunk is not just about configuration — it’s about understanding:
- Alert lifecycle
- Security API permissions
- Event streaming architecture
- Enterprise scalability
- Governance controls
By implementing Continuous Export with automation and aligning it with Splunk’s Microsoft Security Add-on, organizations can achieve real-time, scalable, and audit-ready security monitoring.


Leave a Reply